Installing a Hacking OS in 4 steps
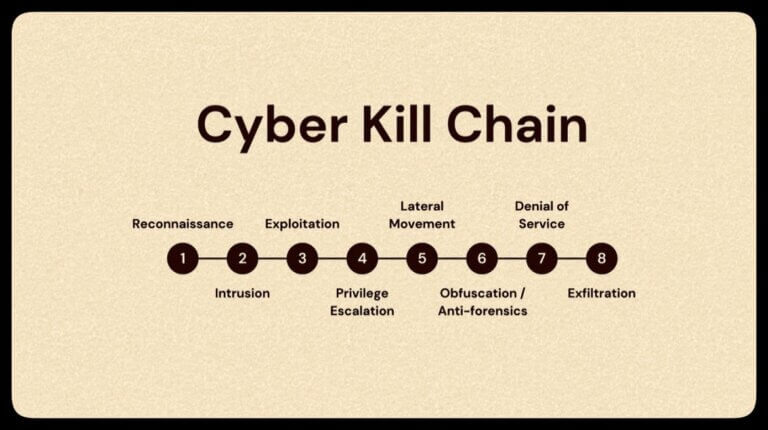
Cyber security is ever-changing, and choosing the best OS with the right toolkit is crucial for ethical hackers and security pros who want to sharpen their skills. Hacking Lab To set up a hacking lab, you will need a pre-installed attacker machine such as Parrot OS, Kali Linux, CommandoVM, BlackArch, or others with the toolkit to scan,…