Web Application Security Best Practices
Web Application Security is an important topic in 2025 because every modern business relies on web applications to manage operations, deliver services online, or engage customers.
Understanding Common Web Apps Vulnerabilities
Web Application Security is critical for protecting data and maintaining trust. An attacker needs to find only one vulnerability in a login form, API, or database to exploit the system and steal sensitive information. Such a thing can damage the business’s reputation and cause long-term damage affecting the customer trust, the stock market, etc.
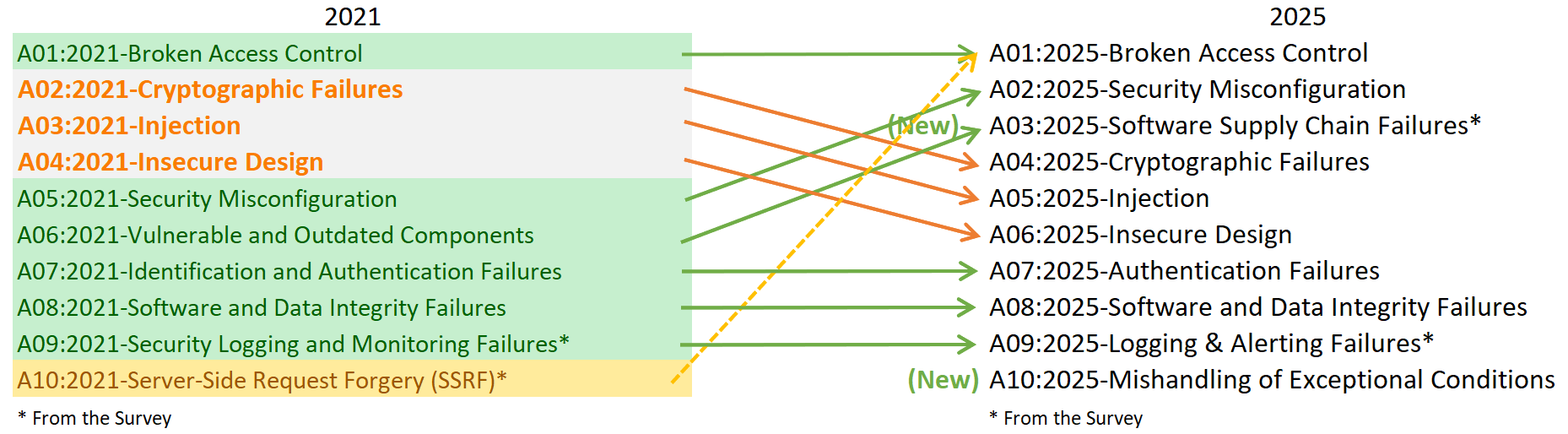
To understand common web application vulnerabilities, we need to go to the OWASP Top 10, which is a standard awareness document for developers and web application security. It represents a broad consensus about the most critical security risks to web applications. The OWASP Top 10 is the most reliable framework for identifying and mitigating risks such as SQL injection (SQLi), cross-site scripting (XSS), cross-site request forgery (CSRF), and broken authentication.
Web Application Security Best Practices
Every web application carries potential weak points that attackers can exploit, and building a secure web application requires more than patching systems after deployment. To create secure web apps, it must all start at the planning stage and continue throughout the entire development cycle.
1. Adopt a Secure Development Lifecycle (SDLC) as shown below.
– Integrate security into every stage of the development lifecycle by embedding processes such as secure coding practices, regular code reviews, automated scans, and continuous threat modelling. Utilize a DevSecOps pipeline to ensure early detection and remediation of vulnerabilities before deployment, maintaining a proactive security posture throughout development.
2. Implement Strong Authentication
– Use multifactor authentication (MFA), identity and access management (IAM), and role-based access control to limit exposure.
3. Encrypt Data Everywhere
– Protect data both in transit and at rest by implementing HTTPS with TLS 1.3, enforcing modern cipher suites, and applying strong encryption algorithms such as AES-256 or ChaCha20. Ensure certificate validation and key management follow best security practices to prevent interception, tampering, and unauthorized access.
4. Validate and Sanitize Input
– Block malicious or unexpected input through strict data validation and sanitization at both client and server sides. Enforce input whitelisting using regular expressions (regex), proper encoding, and content-type checks to prevent common web vulnerabilities such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF).
#Example of RegEx patterns for Input Validations
// Username: 3-20 alphanumeric characters, underscores, and hyphens only
/^[\w-]{3,20}$/
// Email (RFC-compliant basic pattern)
/^[a-zA-Z0-9.!#$%&'*+/=?^_`{|}~-]+@[a-zA-Z0-9](?:[a-zA-Z0-9-]{0,61}[a-zA-Z0-9])?(?:\.[a-zA-Z0-9](?:[a-zA-Z0-9-]{0,61}[a-zA-Z0-9])?)*$/
// Password: at least 8 characters, with uppercase, lowercase, digit, and special char
/^(?=.*[a-z])(?=.*[A-Z])(?=.*\d)(?=.*[@$!%*?&])[A-Za-z\d@$!%*?&]{8,}$/
// URL (http/https only, no javascript: or data: schemes)
/^https?:\/\/(www\.)?[a-zA-Z0-9-]{1,256}\.[a-zA-Z0-9()]{1,6}\b([-a-zA-Z0-9()@:%_\+.~#?&//=]*)$/
// Numeric ID (positive integers only)
/^\d+$/
5. Set Security Headers
– Implement security headers such as Content Security Policy (CSP), HTTP Strict Transport Security (HSTS), and X-Content-Type-Options to mitigate common web exploits. These headers help prevent code injection, enforce secure connections, and restrict content type handling, reducing exposure to attacks like clickjacking, XSS, and data injection.
6. Protect APIs and Endpoints
– Strengthen API security by implementing robust authentication mechanisms using tokens such as JWT or OAuth 2.0, applying rate limiting to prevent abuse, and enforcing strict input filtering and validation. Additionally, ensure proper access controls, encryption of API communications, and detailed logging to detect and mitigate unauthorized or anomalous activity.
7. Conduct Regular Security Testing
– Conduct regular vulnerability scanning, penetration testing, and comprehensive code audits to identify and remediate security weaknesses before they can be exploited. Combine automated tools with manual assessments to uncover complex vulnerabilities, verify the effectiveness of security controls, and ensure continuous improvement of the system’s security posture.
8. Apply Patches and Updates Consistently
– Regularly update all libraries, frameworks, and server components to remediate known vulnerabilities and reduce attack surface. Apply timely security patches, monitor for new updates, and replace unsupported software to close critical security gaps that outdated components can create.
– Automated update management and vulnerability tracking help ensure your environment stays resilient against emerging threats.
OWASP Top Ten Security Vulnerabilities 2025
Basic security is no longer enough; zero-trust architecture verifies every request regardless of origin. For example, every API call requires authentication and authorization based on user identity, device health, and context. Access is limited by least privilege, minimizing lateral movement risks.
#Example: API middleware enforcing zero-trust
def authorize_request(request):
user = authenticate(request.token)
if not user:
return "Access Denied", 401
if not check_device_health(request.device_id):
return "Access Denied - Device Unhealthy", 403
if not authorize(user, request.resource, request.action):
return "Access Denied - Unauthorized", 403
return proceed_with_request(requestOrganizations that embed security into their culture develop more resilient applications. When security informs daily decisions, it evolves from a compliance checkbox into an ingrained practice that safeguards users, data, and the company’s reputation. This proactive mindset reduces breaches, simplifies policy enforcement, and builds trust with customers and partners, ultimately supporting long-term business success.
Conclusion
Web application security is the foundation of digital trust, and neglecting it often leads to far greater costs than investing in it upfront. Each layer of an application—from enforcing strong authentication and authorization to applying robust encryption plays a vital role in protecting users and maintaining operational stability. Leading organizations embed security into every phase of development by adopting secure coding standards, conducting regular audits, and implementing continuous monitoring to adapt to emerging threats.
Whether handled in-house or with specialized partners, building security into the development lifecycle safeguards user data, preserves business reputation, and ensures resilience amid evolving risks.
The latest information and call for action
https://www.owasptopten.org/
Thank you for reading.