Threat Hunting & Incident Response

MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a comprehensive framework that provides a structured and organized approach to analyzing and understanding the tactics and techniques of threat actors during a cyberattack. The MITRE ATT&CK framework offers a detailed description of the various stages of a cyberattack, from initial reconnaissance and exploitation to command and control and lateral movement.
The framework is divided into two main sections: tactics and techniques.
Tactics describe the overarching goals of a cyber attack, while techniques describe the specific methods used to achieve those goals. MITRE regularly updates and maintains the framework, with the latest version (V9.0) including over 250 tactics and techniques categorized into 12 tactics and 15 sub-tactics.
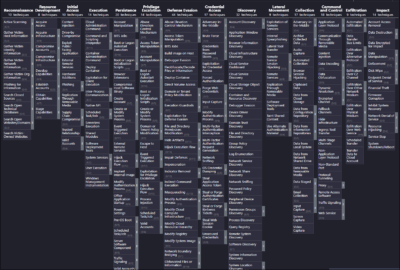
Each tactic and technique is assigned a unique identifier and described in detail in the MITRE ATT&CK matrix. One key strength of the MITRE ATT&CK framework is that it provides a common language for cybersecurity professionals to discuss and share information about cyber threats.
This enables organisations to understand better the tactics and techniques used by attackers and to develop more effective defences. The framework is also helpful in conducting red team exercises, which are simulated attacks carried out by an organisation’s cybersecurity team to identify weaknesses in their systems.
The Red Team can emulate real-world attack scenarios and help organisations identify and remediate vulnerabilities before they can be exploited by real threat actors.
By analyzing the tactics and techniques used by threat actors in the past, organisations can identify patterns and trends, helping them predict and prevent future attacks.
#Introduction to MITRE ATT&CK
- One technique under the ‘Impact’ tactic is –> ‘Data Destruction’
- Lateral Movement occurs –> after ‘Discovery.
- An attacker can use as many techniques –> from each tactic of the ATT&CK® matrix as is required.
- Both red and blue teams –> will benefit from using the ATT&CK® matrix
- ‘Exfiltration Over C2 Channel’ is part of –> the ‘Exfiltration’ tactic
- ‘Hijack Execution Flow’ falls under –> ‘Persistence’, ‘Privilege Escalation’, and ‘Defence Evasion’
- ‘Credential Access’ occurs –> before ‘Discovery’
- After ‘Initial Access’ –> ‘Execution’ is the next tactic
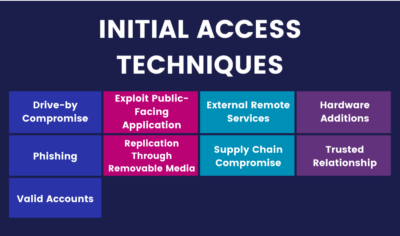
#Tactics: Initial Access
- Network segmentation can prevent access to sensitive resources.
- Many organizations using the SolarWinds® Orion® software were breached due to a supply chain compromise.
- Anti-spoofing and email authentication mechanisms may protect you from phishing attacks.
- Applications with internet-accessible open sockets may be vulnerable to exploitation for initial access.
- File integrity monitoring (FIM) can help detect tampered files.
- Packet sniffing can reveal artifacts related to exploit traffic.
- Generally, targeted phishing is referred to as spearphishing.
- Adversaries may use phishing links and attachments to execute malicious code.
- Technology, such as network intrusion detection systems (NIDS) and firewalls, relies on preset values and algorithms to detect and mitigate attacks.
#Tactics: Execution
- Which of these can allow you to run applications in isolation? Virtualization, micro segmentation
- Which of these may be used on victims to get them to execute malicious code? social engineering
- Which of these may analyze encrypted or compressed files for hidden malware? Download Scanning devices.
- Which of these is not an Execution technique? External remote services
- Exploits that allow remote code execution may be leveraged for what? Remote Access.
- Which of these may specifically be used to stop adware? Adblockers
- Which of these may be able to detect and stop malicious downloads? NIDS/NIPS
- Which of these may adversaries run exploits through? Browsers, Microsoft Office
- What is likely to cause vulnerabilities in software? Insecure coding practices.
- Which of these is a type of command and scripting interpreter that an adversary may use to execute malicious scripts, binaries, and commands? PowerShell
#Tactics: Persistence
- External remote services –> may be abused to maintain access at a network level.
- Adversaries using persistence techniques –> may leave artifacts behind
- Segmenting your network –> may prevent direct remote access
- Unnecessary remote services –> may be disabled
- System-level processes –> may be created or modified to execute malicious payloads repeatedly.
- Write access to system-level process files and logon scripts –>
#Tactics: Privilege Escalation
- Which concept helps detect and mitigate disturbances to the order in which a program’s code is executed? control-flow integrity
- Which of these is not a Privilege Escalation technique? file and directory permissions modification
- What is a vulnerability that’s unknown to vendors and legitimate parties called? Zero-day
- Within which technique may screensavers be leveraged? Event-trigger execution
- Which of these commands sets you as the owner of the software, enabling you to run it with elevated permissions? setuid, setgid
- Adversaries may exploit vulnerable drivers to execute code in what mode? kernel
Only the admin, system, or root may be compromised for higher permissions. False
- Which command can you set an immediate password timeout for so a password is required every time it’s run? Sudo
- Which of these is a security application for Windows that may mitigate exploitation behavior? windows defender exploit guard, enhanced mitigation experience toolkit.
- Which concept helps detect and mitigate disturbances to the order in which a program’s code is executed? Event –
#Tactics: Defense Evasion
- Adversaries can’t disable command history logs? False
- Is the use of third-party software a Defence Evasion technique? False
- Defense Evasion has the most techniques out of all the tactics in the framework? True
- Are security systems always able to monitor inside virtual machines? False
- Are hidden files and directories always checked during system analysis? False
- You may keep system logs at a separate location in case adversaries delete them from your system? True
- Defense Evasion techniques may also be used to hide from investigations after the attack is over? True
- System files are often legitimately modified outside of updates and patches? False
- Adversaries may be able to disable security tools even if they’re native to the operating system? True
- Masquerading is a Defence Evasion technique in which an adversary’s artifacts are passed off as something benign? True
#Tactics: Credential Access
- Input capture –> can involve the interception of keystrokes
- NIST –> has guidelines that can help you decide on password policies for better security
- Legitimate tools –> may be used nefariously by adversaries
- Password policies –> are essential in protecting from various types of credential access attacks
- Network sniffing –> involves the monitoring of wireless or wired traffic
- Brute force –> can involve trying the same password on multiple accounts
- Unique, long, and complex passwords –> can render brute force attacks useless