Caido – A lightweight web security auditing toolkit
Caido – A lightweight web security auditing toolkit
Caido is a new lightweight web security auditing toolkit designed to make professional-grade security testing more accessible. Since it provides a free version, it is perfect for new beginners or security students. However, it has some limitations, up to two scopes. The passionate team’s goal behind this project is to help security professionals and enthusiasts audit web applications with ease and efficiency.
Caido is a great BurpSuite competitor and has plenty of features, such as interception of requests in real-time while browsing, resending test endpoints manually, the possibility of creating your encoders/decoders, providing a sitemap with visualization in real-time, and automation.
In addition, it allows users to install plugins easily and with minimal code required, and it introduces HTTPQL, a new query language for hackers.
HTTPQL allows you to filter requests and responses, and it uses the following: Namespace, Field, Operator, Value
It also supports standalone strings without a namespace, field, and operator to search for requests and responses.
Queries encompass multiple filter clauses combining logical operators and logical grouping.
(resp.code.eq:101
OR resp.raw.cont:"smth"
AND req.path.eq:"graphsql")
Logical operators
AND --both the left and right clauses must be true
OR -- either the left or right clause must be true
Logical grouping
Caido supports the priority of operations, with AND having a higher priority than OR as such:
clause1 OR clause2 AND clause3 is equivalent to (clause1 OR (clause2 AND clause3))
clause1 AND clause2 AND clause3 is equivalent to ((clause1 AND clause2) AND clause3)
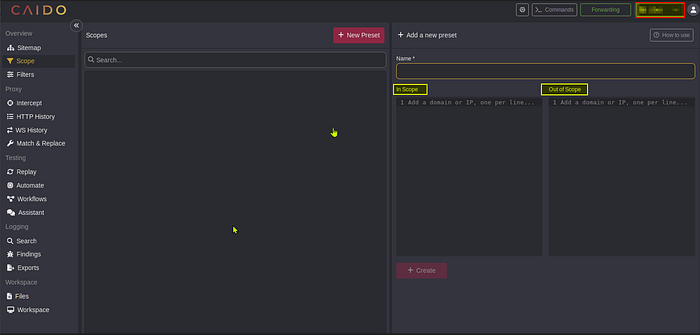
After installing the software, users can indicate which links are considered within the scope and which are not. Additionally, they can easily access the sitemap of any URL requested. The tool allows users to intercept, replay, and view bug reports for specific requests.
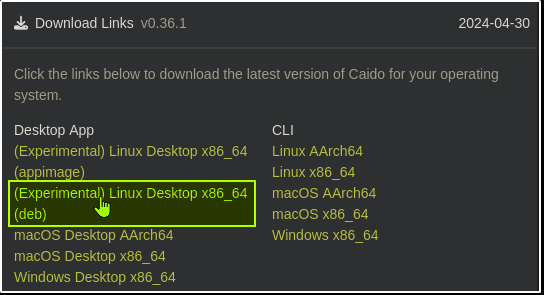
Caido can be installed on macOS, Linux, and Windows. In this article, I will walk you through the installation guide for Linux.
Installing Caido on Linux
First of all, you need to:
- Create an account at caido.io and
- Download the Caido installer package for Linux, which is the deb file from the dashboard or Github repository.
- Open the terminal and navigate to the download package directory.
- Use the command “sudo dpkg i <deb file>” to install Caido.
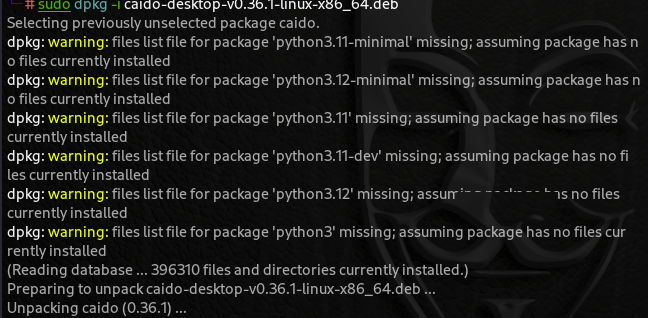
When I first ran this command, I encountered dependency issues, but I was able to fix them by running the “sudo apt — fix-broken install” command.

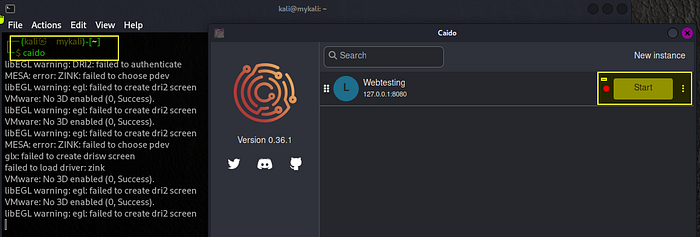
With that in place, the installation was successful. You must type the ” caido ” command in your terminal to launch the software.
A pop-up window indicating that the program runs as it should allows me to edit the instance, which I have named “Web testing,” listening on port 8080.

Caido is a flexible web application security tool. One of its key features is the ability to host it anywhere, such as on a virtual private server (VPS).
By default, Caido listens on the IP address 127.0.0.1 and port 8080. This is the recommended configuration, as there is currently no built-in access control on the proxy portion of Caido. Listening on 127.0.0.1 limits access to the local machine only.
To avoid problems, you must download and set up the CA Certificate provided with the installation.
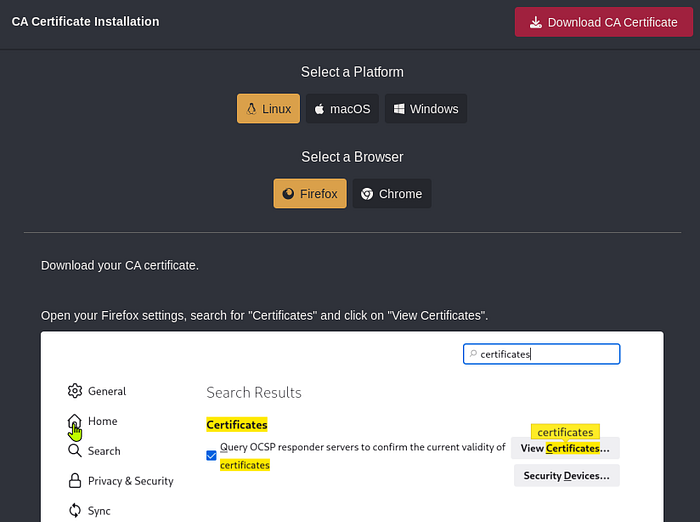
Go ahead and download the certificate. From Firefox settings, search for the certificate you downloaded and click import.
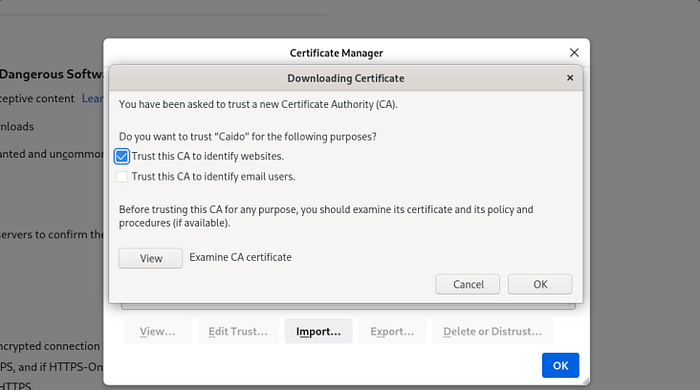
Once it is done, you need to configure your browser’s proxy settings.
You may follow the tutorial here for the installation process.
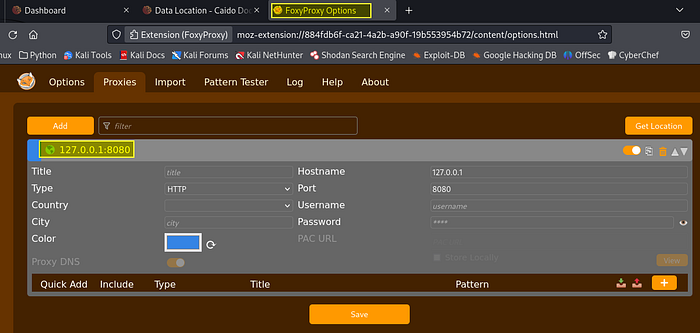
Now click the “Manual Proxy Configuration” radio button. Set the “HTTP Proxy” field to “127.0.0.1” and the “Port” field to 8080. Enable the “Also use this proxy for HTTPS” option.
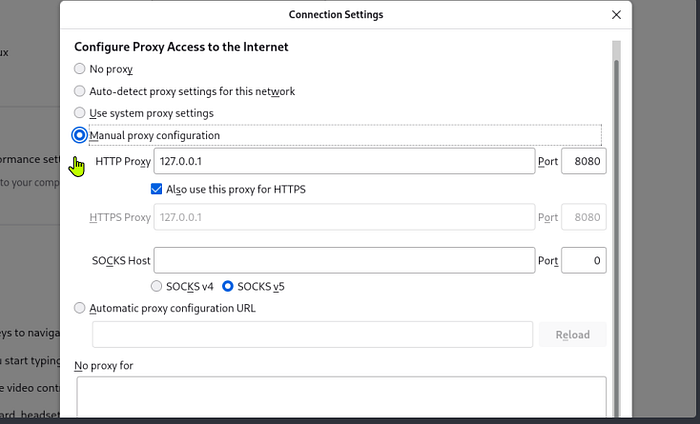
Click “OK” to save the configuration.
You are all set! You can now use Caido.
To start the program after installation, run the command “caido” from the terminal and click start.
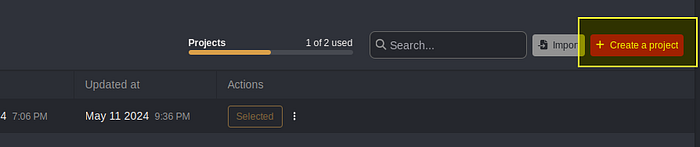
From the top right corner, you can now create a project and define the scope you are interested in. As mentioned above, you have many options here, and from the Scope portal, you can filter domains or IPs that are in or out of scope.
Conclusion
The installation of Caido should be straightforward. Kali Linux is an excellent tool for security assessment, security testing, and vulnerability scanning, containing many tools and utilities.
Caido features
An overview containing sitemap, scope, and filters.
A proxy that intercepts traffic in real-time, HTTP history, WS history, and match & replace.
Testing with the ability to replay, automate, assistant
Logging, which supports search, exports
Workspace for files, up to two projects with the free version, backups
Plugins to expand your tool with custom CSS, custom JS (WIP), and custom workflow nodes (WIP)
Internals such as files, cloud, and authentication